
VMware Releases Critical Patches for Workstation and Fusion Software
[ad_1]
.jpg)
VMware has released an update to address several security flaws affecting its Workstation and Fusion software, the most critical of which could allow local attackers to achieve code execution.
The vulnerability, tracked as CVE-2023-20869 (CVSS score: 9.3), is described as a stack-based buffer-overflow vulnerability that resides in a function to share a Bluetooth host device with a virtual machine.
“A malicious actor with local administrative privileges on the virtual machine could exploit this issue to execute code as a virtual machine’s VMX process running on the host,” the company said. said.
Also patched by VMware is a read out of bounds vulnerability affecting the same feature (CVE-2023-20870, CVSS score: 7.1), which could be abused by a local adversary with admin rights to read sensitive information contained in hypervisor memory from a virtual machine .
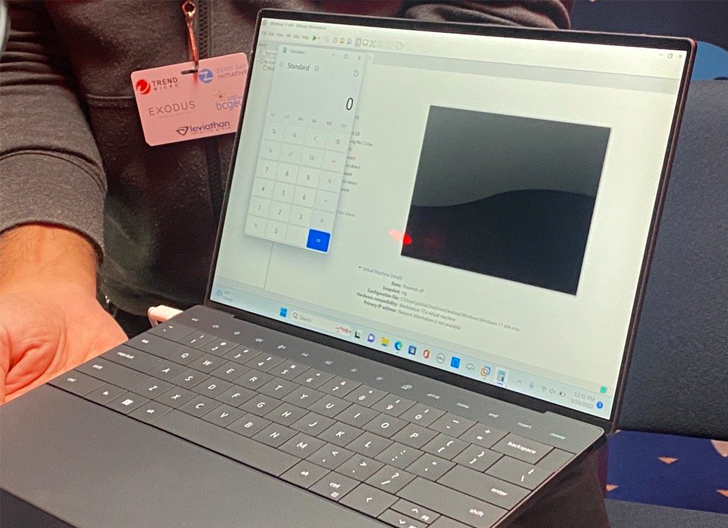
Those two vulnerabilities demonstrated by researchers from STAR Labs on day three of the Pwn2Own hacking contest held in Vancouver last month, earning them an $80,000 prize pool.
VMware has also patched two additional flaws, which include a local privilege escalation flaw (CVE-2023-20871, CVSS score: 7.3) in Fusion and an out-of-bounds read/write vulnerability in SCSI CD/DVD device emulation (CVE-2023-20872 , CVSS score: 7.7).
While the former can enable a bad actor with read/write access to the host operating system to gain root access, the latter can result in arbitrary code execution.
“A malicious attacker with access to a virtual machine that has a physical CD/DVD drive installed and configured to use the virtual SCSI controller may be able to exploit this vulnerability to execute code on the hypervisor of the virtual machine,” VMware said.
This flaw was addressed in Workstation version 17.0.2 and Fusion version 13.0.2. As temporary solution for CVE-2023-20869 and CVE-2023-20870, VMware recommends that users turn off Bluetooth support on virtual machines.
Zero Trust + Deception: Learn How to Outsmart Attackers!
Discover how Fraud can detect advanced threats, stop lateral moves, and improve your Zero Trust strategy. Join our insightful webinar!
As for the CVE-2023-20872 mitigation, it is recommended to remove the CD/DVD device from the virtual machine or configure the virtual machine not to use the virtual SCSI controller.
Development comes less than a week after a virtualization service provider fixed a critical deserialization flaw impacting several versions of Operation Aria for Log (CVE-2023-20864, CVSS score: 9.8).
[ad_2]
Source link






