
Vietnamese Threat Actor Infects 500,000 Devices Using ‘Malverposting’ Tactics
[ad_1]
A Vietnamese threat actor has been implicated as being behind a “malverposting” campaign on social media platforms to infect more than 500,000 devices worldwide over the past three months to present information-stealing variants such as S1deload Stealer and SYS01stealer.
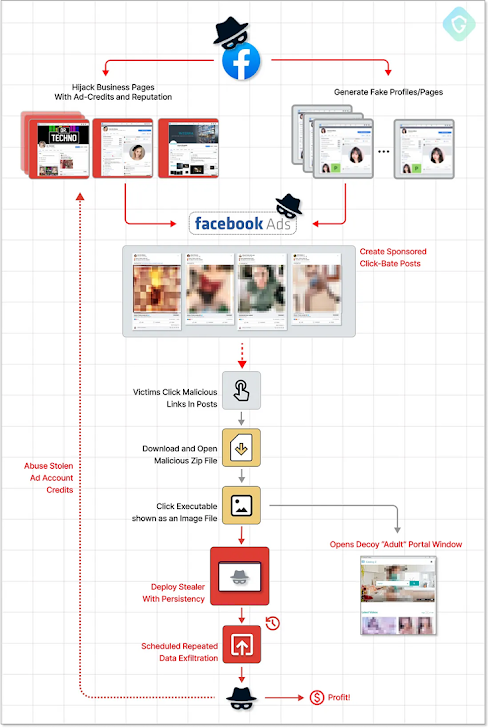
Malverposting refers to the use of social media posts promoted on services such as Facebook and Twitter to mass distribute malicious software and other security threats. The idea is to reach a wider audience by paying for ads to “amplify” their posts.
Based on Guard Laboratorysuch attacks began with adversaries creating new business profiles and hijacking already popular accounts to serve ads claiming to offer free adult-rated photo album downloads.
Inside this ZIP archive file is an image that is claimed to be in fact an executable file, which, when clicked, activates a chain of infection and ultimately spreads thieving malware to suck up session cookies, account data and other information.
This chain of attack is so effective because it creates a “vicious cycle” in which information thieves plunder is used to create an ever-growing army of hijacked Facebook bot accounts which are then used to push more sponsored posts, effectively elevating the scheme further. .
To sneak under Facebook’s radar, threat actors have been found to disguise newly created business profile pages as photographer accounts. Most of the infections have been reported in Australia, Canada, India, the UK and the US
PHP-based rogue deployment methods are said to be continuously evolving to incorporate more detection evasion features, indicating that threat actors behind campaigns are actively refining and retooling their tactics in response to public disclosures.
“Dangerous payloads are quite sophisticated and vary over time, introducing new evasive techniques,” said Guardio Labs security researcher Nati Tal.
Learn How to Stop Ransomware with Real-Time Protection
Join our webinar and learn how to stop ransomware attacks in their tracks with real-time MFA and service account protection.
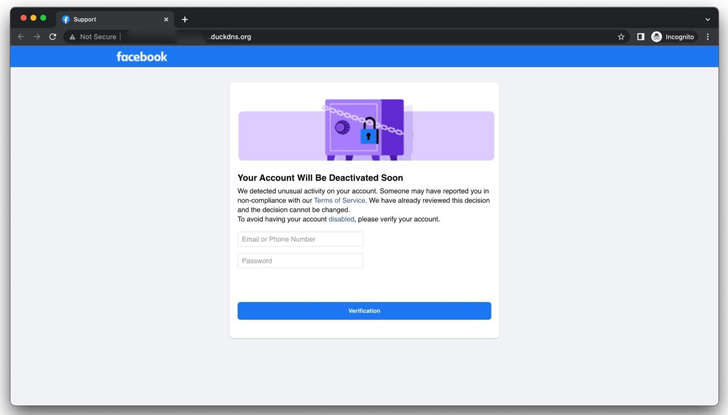
Findings come as Group-IB revealed details of ongoing phishing operations aimed at Facebook users by tricking them into entering their credentials on fake impersonator sites designed to steal their account credentials and take over profiles.
In a related development, Malwarebytes excavated a maladvertising campaign known to trick users who search for games and food recipes on Google into serving malicious ads that redirect them to fake websites created on Weebly with the aim of committing tech support fraud.
[ad_2]
Source link







