
Babuk Source Code Triggers 9 Different Ransomware Strains Targeting VMware ESXi Systems
[ad_1]
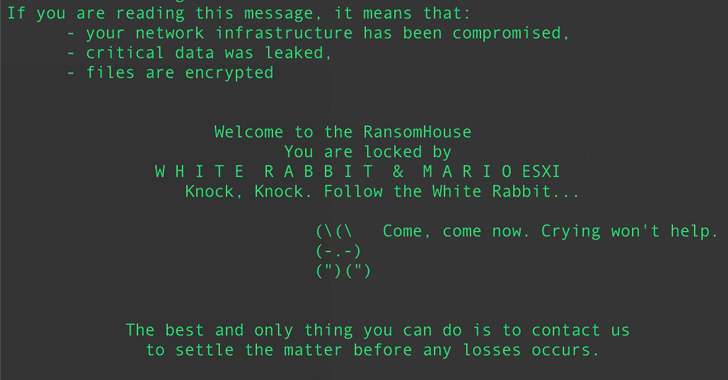
Various threat actors have leveraged the Babuk (aka Babak or Babyk) ransomware code leak in September 2021 to build as many as nine different ransomware families capable of targeting VMware ESXi systems.
“This variant appears through H2 2022 and H1 2023, indicating an increasing trend of adoption of the Babuk source code,” SentinelOne security researcher Alex Delamotte said in a report shared with The Hacker News.
“Leaked source code allows actors to target Linux systems when they may lack the expertise to build a working program.”
a number cyber crime groupCompanies, both big and small, have set their sights on the ESXi hypervisor. What’s more, there are at least three different types of ransomware – CylanceRorschach (aka BabLock), RTM Locker – which appeared early in the year was based on the leaked Babuk source code.
SentinelOne’s recent analysis shows that this phenomenon is more common, with cybersecurity firms identifying source code overlap between Babuk and ESXi lockers associated with Conti and REvil (aka REvix).
Other ransomware families that have ported features from Babuk to their code include LOCK4, DATAF, MarioPlay, and Babuk 2023 (aka XVGV) ransomware.
Despite this apparent trend, SentinelOne said they observed no parallels between the Babuk lockers and ALPHV, Black Basta, Hive, and LockBit ESXi, adding that they found “little similarities” between ESXiArgs and Babuk, suggesting incorrect attribution.
“Based on the popularity of Babuk’s ESXi locker code, actors can also switch to Go-based group NAS lockers,” said Delamotte. “Golang remains the go-to choice for many actors, but its popularity continues to grow.”
Learn How to Stop Ransomware with Real-Time Protection
Join our webinar and learn how to stop ransomware attacks in their tracks with real-time MFA and service account protection.
The development comes as threat actors associated with the Royal ransomware, allegedly former members of Conti, have expanded their attack suite with an ELF variant capable of attacking Linux and ESXi environments.
“The ELF variant closely resembles the Windows variant, and the sample contains no confusion,” Palo Alto Networks Unit 42 said in an article published this week. “All strings, including the RSA public key and ransom note, are stored as plain text.”
Royal ransomware attacks are facilitated through various early access vectors such as phishing callbacks, BATLOADER infections, or compromised credentials, which are then misused to take down Cobalt Strike Beacon as a precursor to ransomware execution.
Since appearing on the scene in September 2022, ransomware Royal has claimed responsibility for targeting 157 organizations at their leak site, with the majority of attacks targeting manufacturing, retail, legal services, education, construction, and healthcare in the US, Canada, and Germany .
[ad_2]
Source link







