
Microsoft Fixes New Azure AD Vulnerability Affecting Bing Search and Main Apps
[ad_1]

Microsoft has patched a configuration issue impacting Azure Active Directory (AAD) an identity and access management service that exposes some “high impact” applications to unauthorized access.
“One of these applications is a content management system (CMS) that powers Bing.com and allows us to not only modify search results, but also launch high-impact XSS attacks on Bing users,” cloud security firm Wiz said in a report. “Such attacks could compromise users’ personal data, including Outlook email and SharePoint documents.”
The issue was reported to Microsoft in January and February 2022, after which the tech giant implemented a fix and awarded Wiz a $40,000 bug bounty. Redmond said found no evidence that misconfiguration has been wildly exploited.
The essence of the vulnerability stems from the so-called “Shared Responsibility Confusion”, where an Azure application could be incorrectly configured to allow users from any Microsoft tenant, leading to a potential case of unintended access.
Interestingly, a number of Microsoft internal apps were found to exhibit this behavior, thereby allowing external parties to read and write to the affected apps.
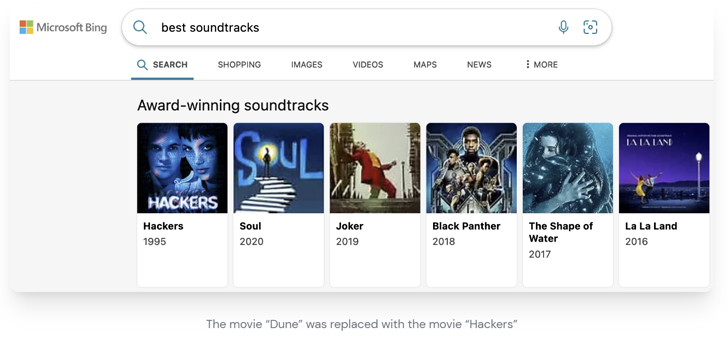
This includes the Bing Trivia app, which the cybersecurity firm exploited to alter search results on Bing and even manipulate content on homepages as part of a chain of attacks dubbed BingBang.

Even worse, an exploit can be weaponized to trigger a cross-site scripting (XSS) attack on Bing.com and extract the victim’s Outlook email, calendar, Teams messages, SharePoint documents, and OneDrive files.
“Bad actors with equal access can hijack the most popular search results with the same payload and leak sensitive data from millions of users,” said Wiz researcher Hillai Ben-Sasson.
Other apps found to be prone to misconfiguration issues include Mag News, Central Notification Service (CNS), Contact Center, PoliCheck, Power Automate Blog, and COSMOS.
Become an Incident Response Pro!
Unlock the secrets to bulletproof incident response – Master a 6-Phase process with Asaf Perlman, Cynet’s Lead IR!
The development comes as the company’s penetration testing company NetSPI revealed details of cross-tenant vulnerabilities in PowerPlatform connector which can be abused to gain access to sensitive data.
After a responsible disclosure in September 2022, the deserialization vulnerability was resolved by Microsoft in December 2022.
This research also follows the release of a patch to restore Super FabriXss (CVE-2023-23383, CVSS score: 8.2), a reflected XSS vulnerability in Azure Service Fabric Explorer (SFX) that can lead to unauthenticated remote code execution.
[ad_2]
Source link






