
Casbaneiro Banking Malware Is Under the Radar with its UAC Bypass Technique
[ad_1]
The financially motivated threat actors behind Casbaneiro banking malware families have been observed using User Account Control (UAC) bypass technique to gain full administrative privileges on the machine, a sign that threat actors are evolving their tactics to evade detection and execute malicious code on compromised assets.
“They are still very focused on Latin American financial institutions, but changes in their techniques are also a significant risk for multi-regional financial organizations,” Sygnia said in a statement shared with The Hacker News.
Casbaneiro, also known as Metamorpho and Ponteiro, is best known for its banking trojan, which first appeared in a mass email spam campaign targeting the Latin American financial sector in 2018.
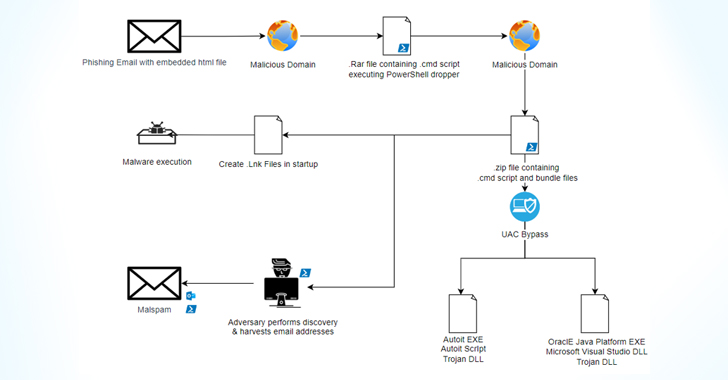
Infection chains usually start with a phishing email pointing to a booby-trapped attachment which, when launched, activates a series of steps that culminate in the spread of banking malware, alongside scripts that utilize living-off-the-land (LotL) techniques to fingerprint hosts and gather system metadata.
Also downloaded at this stage is a binary called Horabot which is designed to spread the infection internally to other unsuspecting employees of the breached organization.
“This adds credibility to the email sent, as there were no obvious anomalies in the email header (suspicious external domain), which would normally trigger an email security solution to act and mitigate,” the cybersecurity firm said in a previous report published in April 2022. “The email included the same PDF attachment used to compromise the previous victim’s host, so the chain was run once again.”
What has changed in the recent wave of attacks is that the attacks began with spear-phishing emails embedded with links to HTML files that redirect targets to download RAR files, a deviation from using malicious PDF attachments with download links to ZIP files.
Protecting Against Insider Threats: SaaS Master Security Posture Management
Worried about insider threats? We are here to help you! Join this webinar to explore practical strategies and secrets to proactive security with SaaS Security Posture Management.
The second major change to the modus operandi concerns usage fodhelper.exe to achieve a bypass UAC and achieve high integrity level execution.
Sygnia said it also observed Casbaneiro attackers creating a dummy folder at C:\Windows(space)\system32 to copy the fodhelper.exe executable, though the specially crafted path is said to have never been used in the intrusion.
“It is possible for an attacker to deploy mock folders to bypass AV detection or to leverage that folder to side-load DLLs with Microsoft signed binaries to bypass UAC,” the company said.
This development marks the third time the mock trusted folder approach has been detected in the wild in recent months, with the method used in the campaign delivering a malware loader called DBatLoader as well as remote access trojans such as Warzone RAT (aka Ave Maria).
[ad_2]
Source link






