
Expert Reveals Identity of Suspected Cyber Crime Kingpin
[ad_1]

Cybersecurity researchers have unmasked the identity of one of the individuals believed to be linked to an e-crime perpetrator known as VEHICLE Group.
Based on Menlo Securitywho gathered information from various online sources, “Nguyen Huu Tai, who also goes by the names Joe Nguyen and Thanh Nguyen, has the strongest possibility of being involved with XE Group.”
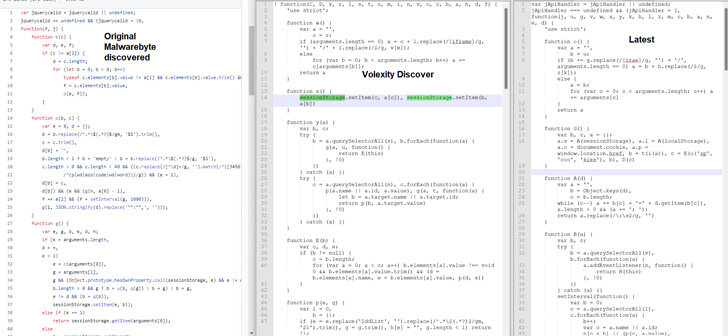
XE Group (aka XeThanh), previously documented by Malwarebytes And Volexityhas a history of carrying out cybercrime activities since at least 2013. Suspected as a threat actor from Vietnam.
Some of the entities targeted by threat actors include government agencies, construction organizations and the healthcare sector.
It is known to compromise internet exposed servers with known exploits and monetize intrusions by installing password stealing or credit card skimming codes for online services.
“As far back as 2014, threat actors were seen creating AutoIT script which automatically generates rudimentary emails and credit card validators for stolen credit cards,” the cybersecurity firm said.
Earlier this March, US cybersecurity and intelligence authorities disclosed XE Group’s attempts to exploit a three-year-old critical security flaw in Telerik’s Progress device (CVE-2019-18935, CVSS score: 9.8) to gain a foothold.
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover untapped vulnerabilities in your API ecosystem and take proactive steps towards tight security. Join our insightful webinar!
Adversaries have also attempted to gain access to corporate networks in the past via phishing emails sent using deceptive domains impersonating legitimate companies such as PayPal and eBay.
In addition to disguising .EXE files as .PNG files to avoid detection, certain attacks use web shells dubbed ASPXSpy to gain control over a vulnerable system.
“XE Group remains a continuing threat to a variety of sectors, including government agencies, construction organizations, and healthcare providers,” the researchers said.
[ad_2]
Source link






