
YouTube Video Distributing Aurora Stealer Malware via Highly Evasive Loader
[ad_1]
Cybersecurity researchers have detailed the inner workings of a highly evasive loader named “in2al5d p3in4er(read: invalid printer) used to deliver Aurora information-stealing malware.
“Loader in2al5d p3in4er compiled with Embarcadero RAD Studio and targeting endpoint workstations using advanced anti-VM (virtual machine) techniques,” cybersecurity firm Morphisec said in a report shared with The Hacker News.
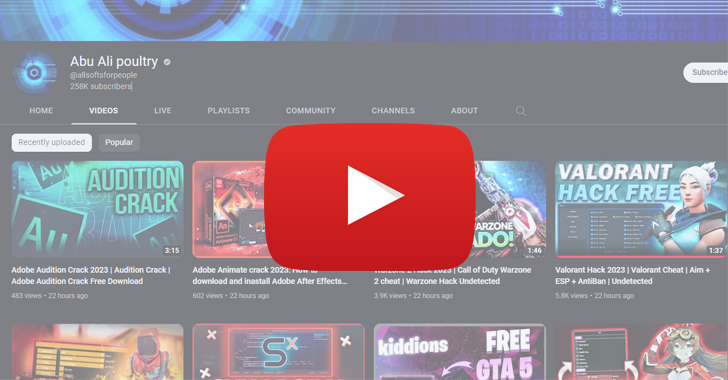
Aurora is a Go-based information stealer that emerged on the threat landscape in late 2022. Offered as commodity malware to other actors, it is distributed via YouTube videos and SEO-ready fake cracked software download websites.
Clicking on links present in YouTube video descriptions leads victims to bait sites where they are tempted to download malware under the guise of apparently legitimate utilities.
The loaders analyzed by Morphisec are designed to query the vendor IDs of the graphics cards installed on the system, and compare them to a set of allowed vendor IDs (AMD, Intel, or NVIDIA). If the values don’t match, the loader stops itself.
The loader finally decrypts the final payload and injects it into an authorized process called “sihost.exe” using a technique called punching process. Alternatively, some sample loaders also allocate memory to write the decrypted payload and run it from there.
“During the injection process, all sample loaders resolve the required Win APIs dynamically and decrypt these names using the XOR key: ‘in2al5d p3in4er,'” security researchers Arnold Osipov and Michael Dereviashkin said.

Another important aspect of the loader is the use of Embarcadero RAD Studio to generate executables for multiple platforms, thereby allowing it to evade detection.
“Those with the lowest detection rates on VirusTotal were compiled using ‘BCC64.exe,’ the new Clang-based C++ compiler from Embarcadero,” said the Israeli cybersecurity firm, demonstrating its ability to circumvent sandboxes and virtual machines.
“This compiler uses different codebases such as the ‘Standard Library’ (Dinkumware) and ‘Runtime Library’ (rt-compiler) and generates optimized code that changes the entry point and flow of execution. This breaks indicators of security vendors, such as signatures composed of ‘malicious/suspicious code block.'”
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – Join this expert-led webinar!
In summary, the findings show that the threat actor behind in2al5d p3in4er utilized social engineering methods for high-impact campaigns that used YouTube as a malware distribution channel and redirected viewers to convincing-looking fake websites to distribute thieving malware.
The development comes as Intel 471 digs into another malware loader AresLoader which is marketed for $300/month as a service for criminals to encourage information thieves masquerading as popular software using binding tools. The loader was allegedly developed by a group associated with Russian hacktivism.
Some of the leading malware families spreading using AresLoader since January 2023 include Aurora Stealer, Laplast Clipper, Lumma Stealer, Stealc, and SystemBC.
[ad_2]
Source link






